Washington State Public Utility
We found that Tenable understood cybersecurity from an industrial control system perspective, not just an IT perspective. And that’s what really drew us to them.
Tenable OT Security
The unified security solution for converged OT/IT environments
Tenable OT Security is a security solution that helps organizations protect their industrial networks from cyber threats, malicious insiders, and human error. It provides visibility into IT, OT, and IoT assets, and helps organizations prioritize cybersecurity risks.
Public Utility District #1 of Whatcom County (WPUD) has countywide authority to provide electric and water services. It currently supplies an average of 27 megawatts of energy to its load customers in the county. WPUD’s electric system consists of 15 miles of transmission and distribution lines and three substations.
Aware of the growing need to protect its critical infrastructure from cyberattacks and insider threats, WPUD sought an industrial- oriented cybersecurity solution that would give it better visibility and control of its OT network.
Key business needs
The Public Utility District #1 of Whatcom County (WPUD) must protect the operational technology (OT) network against cyberattacks that could potentially lead to equipment failures and power outages. The security team required an OT solution that delivered full visibility and alerts on any changes made to controllers and other key devices in its transmission and distribution environments.
With Tenable OT Security, WPUD now has a comprehensive view of cyber risk across their OT operations. They gained visibility into all network traffic through continuous packet capture, improved cyber readiness against remote, local and insider threats, and boosted accuracy through flexible policies and alerts that prioritize real threats.
Challenges
Over the past 15 years, WPUD has modernized its electric substations and water plants to streamline operational efficiency. However, the introduction of digitized control systems with remote access and connectivity to IT networks has also raised the exposure of WPUD’s operational technology (OT) network to cyberattacks that could potentially lead to equipment failures and power outages.
“Cybersecurity has always been one of our concerns, both on the IT side and the OT side,” said Paul Siegmund, manager of automation and technology services at WPUD. “We were looking for a solution that could protect us from both remote and local attacks, including insider threats.” WPUD’s industrial controllers are the crown jewels of its operational network. To ensure service continuity, WPUD required full visibility and alerts on any changes made to controllers and other key devices in its transmission and distribution environments.
The ability to constantly monitor and capture network packets was another key requirement for WPUD. The open-source tools previously used by WPUD for packet analysis were cumbersome and inconvenient to set up, which hindered its troubleshooting of network-related issues.
Solution
Tenable OT Security was initially deployed within WPUD’s industrial control system (ICS) network in 2016, providing Siegmund and his team with complete visibility and control over WPUD’s critical operations. Since then, WPUD has benefited from the addition of new features that have further enhanced the product.
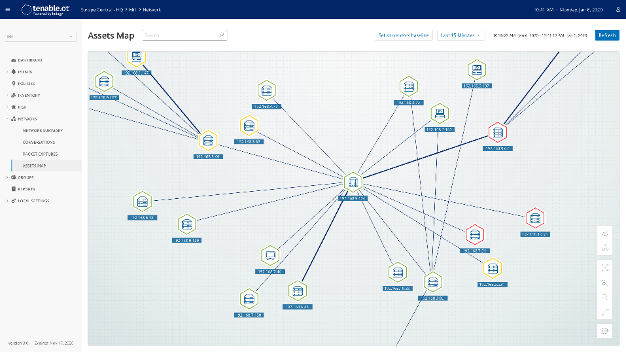 Illustrative data: Tenable OT Security provides a simple-to-use mapping of all OT assets to help you effectively remediate cyber risks.
Illustrative data: Tenable OT Security provides a simple-to-use mapping of all OT assets to help you effectively remediate cyber risks.Comprehensive threat detection
Using Tenable OT Security, WPUD can detect and receive alerts on threats coming from external (e.g., malware) and internal sources. Tenable OT Security identifies anomalous network behavior, enforces network security policies and tracks local changes on devices so that WPUD is always aware of any threat to its ICS environment. Context-aware alerts with detailed information, as well as a comprehensive audit trail, allow WPUD to quickly mitigate cyberattacks and malfunctions that could impact service continuity or people’s safety.- Automated asset tracking
Tenable OT Security automated asset tracking provides WPUD with comprehensive visibility, security and control over its ICS environment. The system gathers and tracks all device-related activities, creating an up-to-date inventory of WPUD’s controllers and assets, including dormant devices. Tenable OT Security automatically maps all controllers and devices on the network, documents their configuration, and provides in-depth visibility into their state. This includes complete controller code snapshots, with detailed version history, to meet WPUD’s backup and recovery needs. - Audit trail
Tenable OT Security can be set to perform continuous packet capture, as well as provide WPUD with a comprehensive audit log detailing all engineering activities related to its controllers. By capturing the who, what, when, where and how, this auditing capability lets WPUD engineers quickly discover the root cause, identify the responsible party and facilitate remediation. - Policy-based detection
WPUD is using the Tenable OT Security policy-based detection feature to configure its own customized security rules in minutes. Using a flexible, wizard-based interface, WPUD can modify the pre-defined “best practice” policies or create new ones as needed. Together with anomaly-based detection, these flexible rules help WPUD effectively enforce its ICS network security policies against any type of threat, as well as significantly reduce the number of alerts.
Impact
- Control of all controllers
Tenable OT Security lets WPUD’s engineers know exactly what’s happening in their network at all times. Using both passive and active detection technologies, Tenable OT Security automatically tracks every configuration and code change in WPUD’s ICS environment – whether performed remotely or locally – along with detailed version control. “The Tenable OT Security product assures me that the firmware and the program that’s in my controller is what I installed, and that nothing’s changed since then,” said Siegmund. - Flexibility and ease of use
WPUD is using the intuitive Tenable OT Security policy configuration tool to set up security policies specific to its own environment. For example, any time the programmable logic controller (PLC) code changes, WPUD engineers receive an alert with full activity information. Beyond that, the tool allows WPUD to create new policies so they don’t get inundated with alerts that aren’t important. “The flexibility for configuring the policies is great. It’s easy to set up. You don’t have to understand fancy rules like you do with most firewalls,” said Siegmund. - Faster response times
Prior to deploying Tenable OT Security, each time WPUD encountered a sticky network problem, it had to set up complicated mirroring and then hook up other tools to profile network traffic and analyze packets. With Tenable OT Security, WPUD performs continuous packet captures which makes it easier for analysts to troubleshoot network events or system alerts.
Conclusion
WPUD selected Tenable OT Security after an extensive evaluation process. “We probably researched 10 or 20 different vendors before we found what we were looking for,” said Siegmund.
Tenable OT Security has now enabled WPUD to obtain a comprehensive view of cyber risk across their OT network.
In one case, WPUD suspected that a rogue machine had been plugged into its network. Using the Tenable OT Security interactive asset map, analysts were able to quickly see all the different assets the suspicious machine was communicating with to make sure its controllers were not compromised.
- Tenable OT Security
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success